Vnc Client On For Tightvnc
VNC® Connect consists of VNC® Viewer and VNC® Server. Download VNC® Viewer to the device you want to control from, below. Make sure you've installed VNC® Server on the computer you want to control. VNC client on the Android device: androidVNC used here; In ConnectBot, connect to the desired machine. Tap the options key, select Port Forwards and add a port: Type: Local Source port: 5901 Destination: 127.0.0.1:5901 In androidVNC connect to the VNC port, this is the local address following the SSH connection. TightVNC is an improved version of VNC, great free remote-desktop tool. The improvements include bandwidth-friendly 'Tight' encoding, file transfers in the Windows version, enhanced GUI, many bugfixes, and more. TightVNC Java Viewer a remote control program that written in Java programming language. It connects to any remote VNC enabled box where Java is installed and lets you control and manage with your mouse and keyboard right from the web browser, just like you sitting in front of the computer.
Royal TS gained support for VNC connections a couple of years ago by integrating with external VNC viewer apps (like Ultra VNC and TightVNC). For a long time, this was the only option because of the lack of good VNC components or SDKs which were affordable and allowed commercial usage. GlavSoft, the creator of TightVNC, now offers an SDK and we immediately decided to implement it. It’s also now the new default plugin for VNC connections (you can, of course, revert back to the previous VNC plugin).
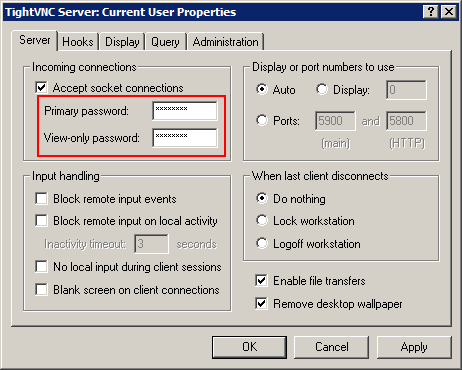
Integrated TightVNC Settings
As known from the previous VNC plugins, the main page allows you to setup the computer name (IP or host name) and the VNC port (default is 5900).
The Advanced settings can be used to control the Encoding, Scaling, Compression, Quality and settings like Clipboard Redirection:
The Input settings page allows you to configure Interaction Mode (Mouse, Keyboard or both), Mouse Tracking and whether or not to show the local cursor.
Pre-Requisites
Unlike the previously available VNC plugins, the integrated TightVNC plugin does not require you to install a VNC viewer executable but it does require the Visual C++ 2010 SP1 runtime installed on your system. Unfortunately, Microsoft doesn’t ship this runtime by default and it needs to be downloaded and installed. The good news is however, this is a very common requirement and chances are that it’s already installed on your machine. In any case, should the runtime not be installed, you will see the following dialog appear:
If you don’t see a green check mark, just click the Download button(s). This will open the Microsoft download page for the necessary files and allows you to quickly install the requirements. Once the installation finished, the green check marks should appear. Clicking OK will then establish your connection.
Actions Tab
While you work with an established VNC connection, you can use the Actions tab to change settings of your connection. In the Scaling group you can choose from 3 different scaling modes: Stretch (keep aspect ration), * Stretch and No Scaling. You can Send Ctrl+Alt+Delete to the remote computer. Additionally you can switch Clipboard Redirection on and off as well as configure whether or not to show the Local Cursor.
TigerVNC is an implementation of the Virtual Network Computing (VNC) protocol. This article focuses on the server functionality.
Installation
Install the tigervnc package.
Running vncserver for virtual (headless) sessions
Initial setup
For a quick start, see the steps below. Users are encouraged to read the vncserver man page for the complete list of configuration options.
- Create a password using
vncpasswdwhich will store the hashed password in~/.vnc/passwd. - Edit
/etc/tigervnc/vncserver.usersto define user mappings. Each user defined in this file will have a corresponding port on which its session will run. The number in the file corresponds to a TCP port. By default, :1 is TCP port 5901 (5900+1). If another parallel server is needed, a second instance can then run on the next highest, free port, i.e 5902 (5900+2). - Create
~/.vnc/configand at a minimum, define the type of session desired with a line likesession=foowhere foo corresponds to which ever DE is to run. One can see which DEs are available on the system by seeing their corresponding.desktopfiles within/usr/share/xsessions/.
For example:
Starting and stopping tigervnc
Startvncserver@.service and optionally enable it to run at boot time/shutdown. Note that the display number needs to be specified following the literal @ sign. For :1 it would look like this:
/usr/bin/vncserver are not supported as they will not establish a proper session scope. The systemd service is the only supported method of using TigerVNC. See: Issue #1096.Expose the local display directly
Tigervnc comes with libvnc.so which can be directly loaded during X initialization which provides better performance.Create a following file and restart X:
Running x0vncserver to directly control the local display
tigervnc also provides x0vncserver which allows direct control over a physical X session. After defining a session password using the vncpasswd tool, invoke the server like so:
For more information, see x0vncserver(1).
Note:- x11vnc is an alternative VNC server which can also provide direct control of the current X session.
x0vncserverdoes not currently support clipboard sharing between the client and the server (even with the help ofautocutsel). See: Issue #529.
Starting x0vncserver via xprofile
A simple way to start x0vncserver is adding a line in one of the xprofile files such as:
Starting and stopping x0vncserver via systemd
In order to have a VNC Server running x0vncserver, which is the easiest way for most users to quickly have remote access to the current desktop, create a systemd unit as follows replacing the user and the options with the desired ones:
Start and enable the service x0vncserver.service in Systemd/User mode, i.e. with the --user parameter.
Running Xvnc with XDMCP for on demand sessions
One can use systemd socket activation in combination with XDMCP to automatically spawn VNC servers for each user who attempts to login, so there is no need to set up one server/port per user. This setup uses the display manager to authenticate users and login, so there is no need for VNC passwords. The downside is that users cannot leave a session running on the server and reconnect to it later.
To get this running, first set up XDMCP and make sure the display manager is running.Then create:
Use systemctl to start and enablexvnc.socket. Now any number of users can get unique desktops by connecting to port 5900.
If the VNC server is exposed to the internet, add the -localhost option to Xvnc in xvnc@.service (note that -query localhost and -localhost are different switches) and follow #Accessing vncserver via SSH tunnels. Since we only select a user after connecting, the VNC server runs as user nobody and uses Xvnc directly instead of the vncserver script, so any options in ~/.vnc are ignored. Optionally, autostartvncconfig so that the clipboard works (vncconfig exits immediately in non-VNC sessions). One way is to create:
Connecting to vncserver
SecurityTypes parameter. With TLSVnc, there is standard VNC authentication and traffic is encrypted with GNUTLS but the identity of the server is not verified. TigerVNC supports alternative security schemes such as X509Vnc that combines standard VNC authentication with GNUTLS encryption and server identification, this is the recommended mode for a secure connection.When SecurityTypes on the server is set to a non-encrypted option as high-priority (such as None, VncAuth, Plain, TLSNone, TLSPlain, X509None, X509Plain); which is ill-advised, then it is not possible to use encryption. When running vncviewer, it is safer to explicitly set SecurityTypes and not accept any unencrypted traffic. Any other mode is to be used only when #Accessing vncserver via SSH tunnels. Any number of clients can connect to a vncserver. A simple example is given below where vncserver is running on 10.1.10.2 port 5901, or :1 in shorthand notation:
Passwordless authentication
The -passwd switch allows one to define the location of the server's ~/.vnc/passwd file. It is expected that the user has access to this file on the server through SSH or through physical access. In either case, place that file on the client's file system in a safe location, i.e. one that has read access ONLY to the expected user.
The password can also be provided directly.
ps on the machine will see it.Example GUI-based clients
- vncviewer-jarAUR
TigerVNC's vncviewer also has a simple GUI when run without any parameters:
Accessing vncserver via SSH tunnels
For servers offering SSH connection, an advantage of this method is that it is not necessary to open any other port than the already opened SSH port to the outside, since the VNC traffic is tunneled through the SSH port.
On the server
On the server side, vncserver or x0vncserver must be run.
When running either one of these, it is recommended to use the localhost option in ~/.vnc/config or the -localhost switch (for x0vncserver) since it allows connections from the localhost only and by analogy, only from users ssh'ed and authenticated on the box. For example:
Make sure to Start or Restart the vncserver@.service, for example (see also #Initial setup):
or for x0vncserver:
On the client
The VNC server has been setup on the remote machine to only accept local connections.Now, the client must open a secure shell with the remote machine (10.1.10.2 in this example) and create a tunnel from the client port, for instance 9901, to the remote server 5901 port. For more details on this feature, see OpenSSH#Forwarding other ports and ssh(1).
Once connected via SSH, leave this shell window open since it is acting as the secured tunnel with the server. Alternatively, directly run SSH in the background using the -f option. On the client side, to connect via this encrypted tunnel, point the vncviewer to the forwarded client port on the localhost.
What happens in practice is that the vncviewer connects locally to port 9901 which is tunneled to the server's localhost port 5901. The connection is established to the right port within the secure shell.
Tip: It is possible, with a one-liner, to keep the port forwarding active during the connection and close it right after:What it does is that the -f switch will make ssh go in the background, it will still be alive executing sleep 10. vncviewer is then executed and ssh remains open in the background as long as vncviewer makes use of the tunnel. ssh will close once the tunnel is dropped which is the wanted behavior.
Alternatively, vncviewer's -via switch provides a shortcut for the above command:
(Notice the double colon – vncviewer's syntax is [host]:[display#] or [host]::[port].)
Connecting to a vncserver from Android devices over SSH
To connect to a VNC server over SSH using an Android device as a client, consider having the following setup:
- SSH running on the server
- vncserver running on server (with
-localhostflag for security) - SSH client on the Android device: ConnectBot is a popular choice and will be used in this guide as an example
- VNC client on the Android device: androidVNC used here
In ConnectBot, connect to the desired machine. Tap the options key, select Port Forwards and add a port:
In androidVNC connect to the VNC port, this is the local address following the SSH connection:
Tips and tricks
Connecting to an OSX system
See https://help.ubuntu.com/community/AppleRemoteDesktop. Tested with Remmina.
Recommended security settings
If not #Accessing vncserver via SSH tunnels where the identification and the encryption are handled via SSH, it is recommended to use X509Vnc, as TLSVnc lacks identity verification.
Issuing x509 certificates is beyond the scope of this guide. However, Let's Encrypt provides an easy way to do so. Alternatively, one can issue certificates using OpenSSL, share the public key with the client and specify it with the -X509CA parameter. An example is given below the server is running on 10.1.10.2:
Vnc Client Ubuntu Tightvnc
Toggling fullscreen
This can be done through vnc client's menu. By default, vnc client's mkey is F8.
Vnc Client Tightvnc
Workaround for mouse back and forward buttons not working
The VNC protocol currently only uses 7 mouse buttons (left, middle, right, scroll up, scroll down, scroll left, scroll right) which means if your mouse has a back and a forward button these are not usable and input will be ignored.
evrouter can be used to work around this limitation by sending keyboard key presses when clicking the mouse back/forward buttons. Optionally xte found in xautomation and xbindkeys can be used on the server to map the keyboard key presses back to mouse button clicks if needed.
Substituting mouse back/forward buttons with keyboard keys XF86Back/XF86Forward
This method is simple and suitable if you only need a way to navigate backward/forward while using web browsers or file browsers for example.
Install evrouterAUR and xautomation on the client. Configure evrouter, see Mouse buttons#evrouter and evrouter man pages for instructions and tips on how to find the correct device name, window name, button names etc. Example config:
Start evrouter on the client. With above configuration keyboard key XF86Back is sent to the VNC server when clicking the back button on the mouse, and XF86Forward is sent when clicking the forward button.
Mapping the keyboard key presses back to mouse button clicks on the server
If needed it's possible to map the keyboard keys back to mouse button clicks on the server. In this case it might be a good idea to use keyboard keys which are never on the client or server. In the example below keyboard keys XF86Launch8/XF86Launch9 are used as mouse buttons 8/9.
Evrouter configuration on the client:
Install xautomation and xbindkeys on the server. Configure xbindkeys to map keyboard keys XF86Launch8/XF86Launch9 to mouse buttons 8/9 with xte.
Start xbindkeys $ xbindkeys -f ~/.xbindkeysrc. The server will now map XF86Launch8/XF86Launch9 to mouse buttons 8/9.
Troubleshooting
Terminals in vncserver start in / (root dir)
This is a known issue introduced upstream. See: https://github.com/TigerVNC/tigervnc/issues/1108
Unable to type '<' character
If pressing < on a remote client emits the > character, try remapping the incoming key [1][dead link 2020-04-03 ⓘ]:
Black rectangle instead of window
Most probably this is due to the application strictly requiring the composite Xorg extension. For example webkit based app: midori, psi-plus, etc.
Restart vncserver in this case using something like following:
It looks like Composite extension in VNC will work only with 24bit depth.
No mouse cursor
If no mouse cursor is visible when using x0vncserver, start vncviewer as follows:
Or put DotWhenNoCursor=1 in the tigervnc configuration file, which is at ~/.vnc/default.tigervnc by default.
Copying clipboard content from the remote machine
If copying from the remote machine to the local machine does not work, run autocutsel on the server, as mentioned in [2]:
Now press F8 to display the VNC menu popup, and select Clipboard: local -> remote option.
'Authentication is required to create a color managed device' dialog when launching GNOME 3
A workaround is to create a 'vnc' group and add the gdm user and any other users using vnc to that group.Modify /etc/polkit-1/rules.d/gnome-vnc.rules with the following[3]:
No window decoration / borders / titlebars / cannot move windows around
Start a window manager to fix an empty xterm frame. E.g. on xfce, run `xfwm4 &` in the terminal.
systemd service unit run as user
Vnc Viewer For Tightvnc
To start service for example on display 9:
You maybe want to enable this at boot: